If your operating system is protected, Ooss Ransomware should not be able to sneak in. However, if you do not use protection tools, and if you are relying on your own ability to identify and remove malware before it is executed, it is unlikely that you will stand a chance of stopping this threat before it encrypts your personal files. Anti-Spyware-101.com researchers warn that this malware uses very sneaky ways to invade your operating system, and you are always involved in the process. For example, the infection’s launcher could be introduced via a bundled downloader as a helpful application. If you are tricked into executing this bundle, the ransomware slithers in immediately. In a different scenario, the launcher could be introduced via spam email as a document/PDF file that, allegedly, represents flight information, hotel reservation, postage delivery details, etc. If you open this file, the ransomware executes. After that, the only thing you can do is delete Ooss Ransomware. Read more »
Monthly Archives: March 2020
Weather Waves
Weather Waves might have useful features, but you should know that it could also have irritating qualities. It is why specialists decided to place this extension in the category of potentially unwanted programs. If you did not know this before, there could be other things that you might not know about this application. Therefore, we encourage you to read our full article. In it, we talk about how this application could be spread, how it may work, and which of its qualities might seem annoying. Also, we explain how users who do not want to keep this potentially unwanted program on their computers could erase it. To make this task even easier, we prepared the removal instructions available at the end of the text that show how to delete Weather Waves from Google Chrome and Mozilla Firefox browsers. Read more »
Righ Ransomware
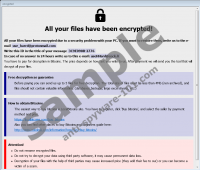
Righ Ransomware is a tremendously clandestine infection that bets on people to be careless with spam emails and bundled downloaders. If you interact with spam email attachments and unreliable downloaders carelessly, you could let the infection in before you know what is going on. The launcher of this malware can be concealed in a clever manner, and you could be tricked into executing it yourself. Once the file is planted, it can do some serious damage. The main task for this malware is to encrypt your personal files, and it can do that successfully using a unique encryption key. A matching decryption key should exist, but you are unlikely to get your hands on it, which is why this kind of malware is so dangerous. Anti-Spyware-101.com research team has analyzed the malicious infection, and our recommendation is that you delete it as soon as possible. Shouldn’t you figure out what to do about the encrypted files first? Well, we hope that you will be able to restore them after you remove Righ Ransomware. Read more »
Remk Ransomware
Remk Ransomware leaves an extension called .remk on the files that it encrypts, which is where its title comes from. The malware encrypts files with a secure encryption algorithm. Meaning, files affected by it cannot be restored unless you have a unique decryption key and a decryptor. While the malware’s developers seem to have such tools, they are willing to share them only with victims who pay ransom. The worst part is that even if you pay the sum they ask and on time, you cannot still be certain that the hackers will hold on to their end of the deal. Therefore, dealing with the malicious application’s creators could make matters even worse if you end up losing your money as well. To learn more about the malware, we recommend reading the rest of this article. Also, since our specialists advise deleting Remk Ransomware, we encourage you to check our removal instructions placed at the end of this page. Read more »
Search Anything
In this article we talk about a browser extension called Search Anything. Due to its working manner, the application was classified as a potentially unwanted program. It is vital to understand that such classification does not mean that the add-on is dangerous. What it means is that it could have undesirable qualities that might make some users want to erase it. Thus, what we recommend is learning more about this extension so you could decide for yourself if you should keep it or not. By reading our report you can find out how it might be spread, how it could work, and how it could be erased. In fact, if you decide to remove Search Anything, you could also check our deletions steps available below that show how to get rid of this potentially unwanted program manually. Read more »
HistorySee
At the first glance, HistorySee might look like a decent educational tool, but in reality, it is a potentially unwanted application. It means that this extension might enter your browser accidentally. If that is really the case, you can scroll down to the bottom of this description for the manual removal instructions. However, you should also consider the possibility that there are more unwanted programs on your computer than just HistorySee. To make sure that your system is absolutely safe, it would be a good idea to run a full computer scan with a licensed security tool of your choice. Read more »
Vista Search
Vista Search might not seem like much of a threat, but it is a potentially unwanted program (PUP). A PUP is not a malicious computer infection. It is a regular program that users often download and install accidentally. You might wonder how on earth that could happen because clearly, people download only the programs they want and need, right? Well, you’d be surprised. It quite often that the likes of Vista Search manage to plop into target systems out of the blue, and then users are left scratching their heads, wondering what happened. And then they scramble to remove Vista Search and all the other unwanted apps. Read more »
Eight Ransomware
Eight Ransomware adds the “.id[{your unique ID}].[use_harrd@protonmail.com].eight” extensions to the files it corrupts. Can you see this extension added? If you can, we suggest taking immediate action. First of all, remove the malicious threat. The damage might be done already, but you want to destroy the infection that has caused it. Second, you want to replace the corrupted files with copies that, hopefully, you have stored online or on external drives. If you do not have copies, you might not be able to restore personal files at all. Finally, you have to get down to the root of the problem, which is Windows security. Clearly, something went wrong for the malicious infection to slither in successfully. Whether your security software has failed, or you did not have any security systems implemented at all, you want to make sure that your system and the remaining files can stay safe in the future. If you want to learn more about how to delete Eight Ransomware, how to replace files, and how to secure Windows, keep reading. Read more »
Lokd Ransomware
Lokd Ransomware is one of those file-encrypting threats that are used for money extortion. As you see, the malicious program enciphers victims’ private files as they could be irreplaceable and then shows a note that asks to pay in exchange for decryption tools. Such tools could be your only way to restore your files, but we do not advise purchasing them if you fear getting scammed and losing your money for nothing. If you want to know more about the malware, we encourage you to read the rest of this article. Also, we can offer our removal instructions that show how to erase Lokd Ransomware manually. You can find our instructions at the end of this page, where you should also find our comments section that you could use if you have any questions about the discussed malicious application. Read more »
NEFILIM Ransomware
NEFILIM Ransomware is a malicious computer infection that will encrypt your files, no questions asked. If this program enters your system, one day, you will find yourself with tons of files that your OS can no longer read. Then what? The infection would want you to pay the ransom fee for the files, but you should never do that. By paying the ransom, you would only encourage these criminals to continue making more infections. You need to remove NEFILIM Ransomware and everything related to this program from your system, and then look for ways to get your files back. Read more »