Scannewsupdate.info is an adware server that works as a redirect on Chrome and Firefox. In order to avoid continuous redirections to this annoying website, you should scan your computer with a licensed antispyware tool to see whether you have any adware program installed on your computer. It would also be a good idea to reset your browser settings to default because you might as well have several unwanted extensions working on your browser. In this entry, we will talk more about adware and adware servers that can be used by malevolent third parties to expose you to potentially harmful content. Read more »
Monthly Archives: January 2019
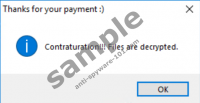
InducVirus Ransomware
Do not leave your Windows operating system vulnerable to the malicious InducVirus Ransomware, also known as Delphi Ransomware. This dangerous infection relies on unprotected systems with security backdoors, and when it invades, the victim is not alarmed at all. The encryption process is silent, and the infection is capable of encrypting files in the %USERPROFILE% directory without any notice. Once they are encrypted, the “.FilGZmsp” extension is added to the names, which should help you see which files were corrupted faster. If you are prepared, your personal files are backed up, and there is nothing you need to worry about. Delete InducVirus Ransomware and then use your backups to access files. If files are not backed up, you might be thinking about contacting cyber criminals – something we discuss in this report – but that is dangerous. In any case, whatever moves you make, you must remove the infection, and the information Anti-Spyware-101.com research team provides will help you with the process. Read more »
Venom Ransomware
Venom Ransomware displays a black window with links to articles about Bitcoins and instructions on how to pay for decryption tool. In exchange, the hackers behind the malware offer a decryptor that is said to recover files encrypted by the threat. The affected files are those that have .venom extension, for example, picture.jpg.venom. Another way to restore these files is to replace them with backup copies from cloud storage, removable media devices, and so on. If you have such an option, we recommend deleting Venom Ransomware right away. In fact, we would advise removing it even if you cannot restore your data, as putting up with the hackers’ demands could be hazardous. If you need instructions on how to eliminate the malicious application, you should check the steps available below. Naturally, to find out more details about the infection, we invite you to read our full article. Read more »
XCry Ransomware
XCry Ransomware is a malicious program that locks private files and marks them with .xcry7684 extension. Such records become unusable without particular decryption tools. Sadly, they are in the hands of hackers who developed the malware, and they demand to be paid before providing them. Needless to say, there are no reassurances these people will hold on to their word, and if you do not want to be tricked, we advise not to put up with any demands. Our researchers think it would be safer to remove XCry Ransomware at once since it can restart with the system, which means it might be able to encrypt new files. To eliminate it manually you should follow the instructions placed at the end of this report. Read more »
ANATOVA Ransomware
ANATOVA Ransomware encrypts user’s data and drops a note called ANATOVA.txt. Inside of this note, the victim should find a text saying the files can be decrypted for 10 Dash. Currently, it is about 658 US dollars. It is a rather high price considering there are no guarantees the user will get what he pays for. Therefore, for those who come across this malicious application, we would advise not to make any rash decisions. It is best to learn more about the threat and only then decide what to do. Our recommended course of action is ANATOVA Ransomware’s deletion. It does not restore encrypted files, but it cleans up the system, and as a result, it becomes safe to transfer backup copies, create new data, and so on. If you decide you want to remove the malware instead of putting up with any demands, we invite you to take a look at the deletion instructions located below. Naturally, for more information about the threat, you should continue reading our report. Read more »
Pro Speed Check
If you think that Pro Speed Check is a terrific tool because it can accurately show your Internet speed, you are mistaken. Anti-Spyware-101.com research team classifies it as a potentially unwanted program, and our recommendation is that you delete it without any delay. Sure, it is not a malicious threat, and so you do not need to act urgently, but note that you will not be safe until this PUP is eliminated. That is because it takes over the browser and modifies the default search provider. Although you can avoid using the default search provider on Google Chrome – the web browser the PUP is compatible with – why tiptoe around something that you can eliminate? If you need help removing Pro Speed Check, you will definitely find information that will help you in this report. If you want to learn more before you take any steps, keep on reading. We understand that not everything in this post might be clear or that you might have questions, which is why we have opened the comments section below. Read more »
CuteRansom Ransomware
Did CuteRansom Ransomware attack your operating system? If it did, your personal files must be encrypted and renamed, and you must have been introduced to a message indicating that files were corrupted using YuAlock. This is an alternative name, but both are equally as valid. This malware works like your regular file-encryptor (e.g., XARCryptor Ransomware or BooM Ransomware), but it is not a cookie-cutter. At the time of research, this infection did not ask for a payment in return for a decryption key or program. In fact, the message created by the treat asked to send an email. This is bizarre, and, unfortunately, it is unlikely that anything can be done to decrypt files. Once they are corrupted, they are practically lost. The situation is not so hopeless if your files are backed up. If they are, you need to delete CuteRansom Ransomware and then figure out how to ensure that this threat – or any other – invades your operating system in the future. Read more »
IRS Online asstmanager@jacktree.com Scam
If you do not want to face a malicious Trojan, IRS Online asstmanager@jacktree.com Scam is the one to look out for. It is important to mention that the email address attached to the scam could be different in your case. One other example is allenyoon@hanmiinc.com. The subject line could be adjusted too. Cyber schemers need to be smart about how they approach victims, and if they continue to use the same addresses, subject lines, and even the messages themselves, they are unlikely to succeed as much. The ever-changing scams make it much harder for security experts to catch them and warn users in time. Unfortunately, the consequences can be dire. If you are not careful and fall for the scam, you might let in malware without even knowing it. According to our research, some victims find that they need to remove IRS Online asstmanager@jacktree.com Scam-related Trojans. One of them is the vicious Emotet Trojan. If you continue reading, you will learn how to recognize the scam and delete malware. Read more »
Normandoh.com
Your browser may start loading Normandoh.com while surfing the Internet if you come across this browser hijacker. The application is not malicious, but it can be annoying, as it may show various advertisements from different third parties. Another thing you ought to be aware of is that some of the threat’s displayed ads could be potentially dangerous, which is why we recommend being extra cautious. Naturally, if you do not want to risk encountering suspicious ads or do not want to see Normandoh.com on your browser, you should erase it with no hesitation. There are a couple of ways to deal with the browser hijacker, and we will explain them further in the text. Moreover, users who are determined to get rid of it manually, but need some guidance can find step by step deletion instructions added slightly below the article. Read more »
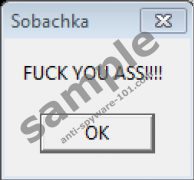
Ransom102 Ransomware
If you see a message saying “You are ransomwared,” you may have encountered a threat we call Ransom102 Ransomware. It locks user’s data on specific directories and then opens a window claiming the victim has to pay if he wants to get his data back. Needless to say, we would not recommend paying anything. First of all, there are various ways the cybercriminals could trick you. Also, it seems the decryption key, needed to unlock all encrypted files, can be extracted from the malicious application. Our researchers at Anti-spyware-101.com report it is Kevi379K. Soon after you encrypt your data with it, we advise not to wait any longer and erase this malicious program from the computer. To learn how to remove Ransom102 Ransomware manually, you should take a look at the instructions available below. Of course, if they appear to be too complicated, you should leave this task to a legitimate antimalware tool. Read more »